Tired of assigning license one by one to the user? With this script you can assign to all or only specific users. But first you need to know what are your License ID in the Azure AD.
*Make sure you have the Azure Power Shell installed to your computer
*Scripts below are modifiable
Here are the steps below;
1. Open Azure Power Shell > Connect to your Office 365 Azure
Connect-MsolService
2. Getting the type of subscriptions
Get-MsolAccountSku

3. Now with the view of subscriptions you have on your office 365, you can now identify which subscription you want to enable for your users. To know which subscription is their actual display name, you could compare it on your Office 365 portal > Subscription details
4. For now we will take AccountSkuID: domain:ENTERPRISEPACK (E3 package) as our example;
*Note: This script will only Add License and it wont remove other existing license that had assigned to the user(with multiple license)
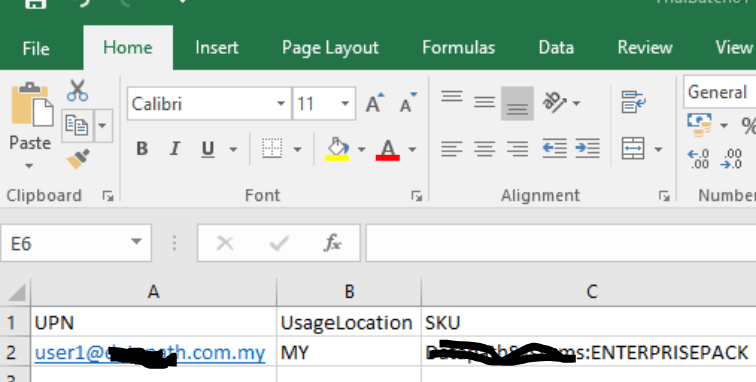
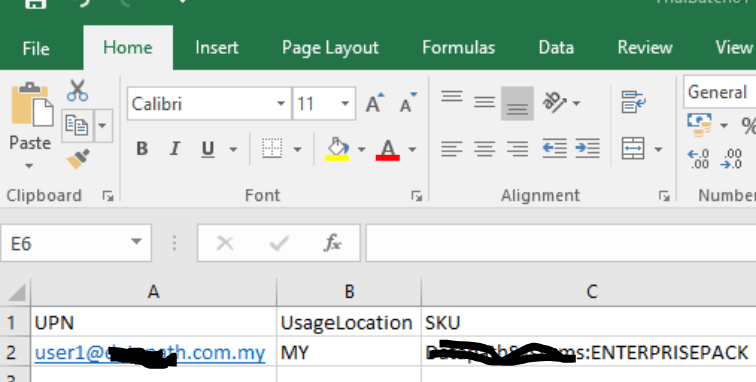
a. This is the method of using the csv file to assign license for the user OR convert users from license A to License B, where the csv file contain columns of UPN, UsageLocation and License that you want to enable for your users
#Get .csv file of users
$users = import-csv .\userList.csv -delimiter ","
#Loop
foreach ($user in $users)
{
$upn=$user.EmailAddress
$usagelocation=$user.UsageLocation
$SKU=$user.SKU
Set-MsolUser -UserPrincipalName $upn -UsageLocation $usagelocation
Set-MsolUserLicense -UserPrincipalName $upn -AddLicenses $SKU
}
This is how inside of the csv looks like;
UPN: User principal Name
Usage Location: Location of country
SKU: License type
b. Or if you want unlicensed users to be assign with license, you could run
Get-MsolUser | where {$_.isLicensed -eq $false} | Set-MsolUser -AddLicenses "domain:ENTERPRISEPACK"
5. To know whether the script works, you could try the below type of reassurance;
a. Get Command, to view whether the once unlicensed user now is already licensed is appearing in the unlicensed list
Get-MsolUser | where {$_.isLicensed -eq $false}
b. You could check in the Office 365 portal by creating a custom view > specific license type
c. You could check in the Office 365 portal by choosing > Unlicensed. To view whether the “Just only licensed user” is in the unlicensed list.