Hi everyone, has been awhile, due to Chinese New Year. Anyway, is good to be back!
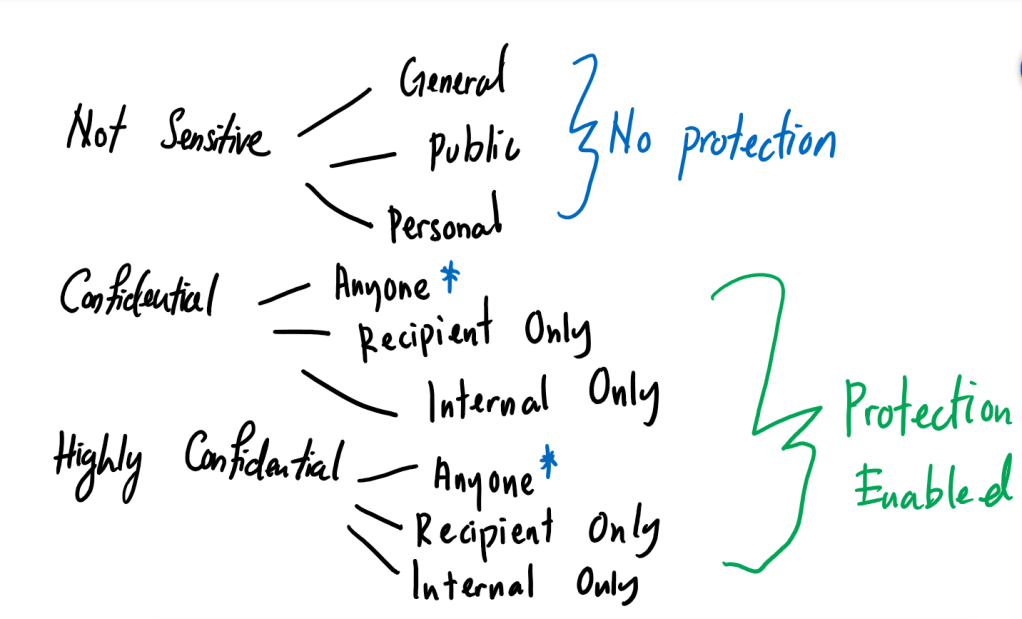
Situation for this issue, is that you have shut down the Microsoft Exchange server and you are in the process of rebranding (Example, changing UPN, email address or Logon), but you encounter that some users having the issue to open their online archiving. Hence, you would like to export their MsExchArchiveGUID from Active Directory and perform a comparison with the Cloud’s Archive GUID instead of turning on the Exchange Server (You do not want to make your effort redundant). However, no matter how you try with this command on your Active Directory, Get-ADUser -Filter * -Properties * | Export-csv filename.csv and you still can’t get them to show up on your csv file.
This article would require review of the reference links.
Don’t panic! All you got to do is:
- Prepare a test PC (OS version of Windows 10 at least) or a server (Non-critical ones, OS version of Windows Server 2012 R2) that is a domain joined
- I would recommend using a test PC, to avoid the hassle of checking whether the Windows Server is critical or notor the hassle of stuck at Exchange Server Wizard (Role Selections)
- Prepare an account that has a domain admin rights.
- Make sure you know what your Exchange Server’s version (Example, CU 2013, CU 2010, CU 2016, or CU 2019).
- If you don’t remember you can always relocate the Exchange Server’s object from your AD. Else, you have to guess.
- Logon the PC with the account that has domain admin rights > Install the RSAT tool onto the PC
- Recommended RSAT tools are: Active Directory Domain Services and Lightweight Directory Services Tools, and Server Manager

- Install IIS 6 Metabase Compatibility and IIS 6 Management Console
- Reboot the PC
- Relogin to the PC with the account that you had logon too, go to browser and search for your Exchange Server CU version and then download the package
- Export/eject the .iso file, run the Setup.exe
- Choose the option of not to allow windows update > Next
- Agree the license agreement > Next
- On Recommended setting page > Choose recommended or not.
- On the Server role Selection > Choose only Management tools > Next
- Location of the installation you can remain with the default
- On Checking the prerequisites page, if you faced any of these errors just follow the instructions on how to resolve them or Google Search how to do it based on your PC’s OS version.
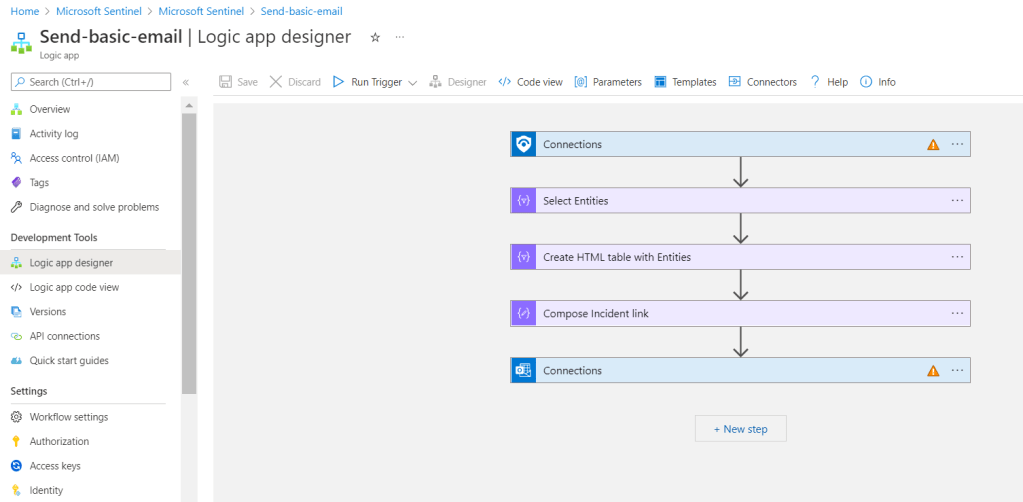
- Once you have successfully downloaded the exchange management tool you can start to export your msExchArchiveGUID
- Once finish remember to revert you configuration to the PC
References:
- https://learn.microsoft.com/en-us/exchange/install-exchange-2013-using-the-setup-wizard-exchange-2013-help
- https://learn.microsoft.com/en-us/exchange/iis-6-compatibility-components-not-installed-longhorniis6mgmtconsolenotinstalled-exchange-2013-help
- https://learn.microsoft.com/en-us/powershell/exchange/filter-properties?view=exchange-ps#archiveguid