Hi fellow friends! Hope you guys are healthy and staying safe. Today’s topic is about Active Directory on-premises.
Why are there default domain policy and default domain controllers’ policy? Is it for me to use it? Can I alter it?
There are still people recommend using default policies. However, what will happen afterwards no one care to know about it.
“What’s the implications?”
“Why can’t I use default policies?”
I do faced challenges when people are telling me “I have been using a separate group policy to manage password and it works.”. To me just saying is just prove nothing. To prove your point, is using Lab environment.
Using group policy to manage different password is not supported, because whatever policy that you created under the child layer/level it will be overwritten by the default policies. Hence, no point.
Based on Microsoft recommendation, any default policy coming from Active Directory, should not be modify or you can keep the modification to minimum, such as enable more audit features. Active Directory is sensitive. Anything that is default remains default.
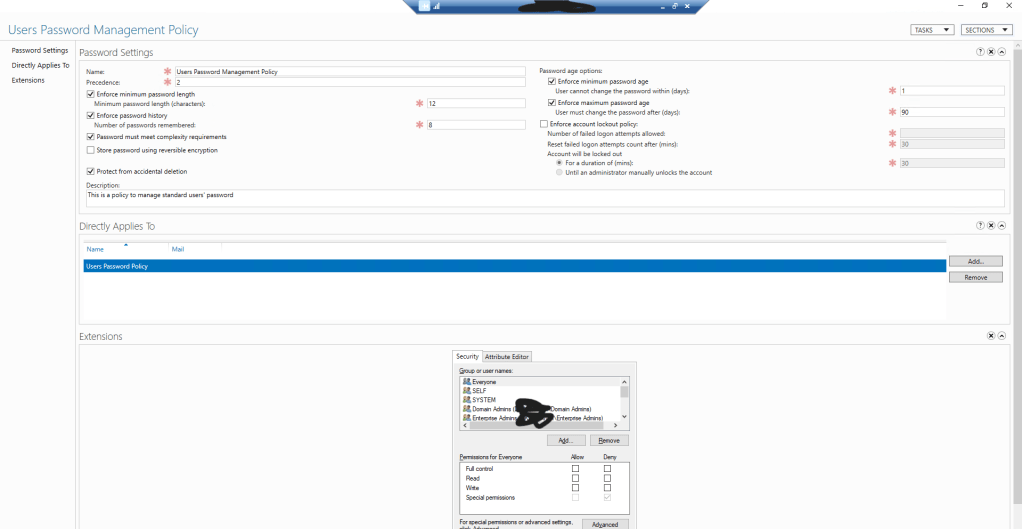
I would recommend using the Fine-Grained Password Policy and/or the LAPS for password management. LAPS has been around for quite some time and Fine-Grained Password too but there are still people not aware about this feature from Active Directory.
Fine-Grained Password policy is great, when you have multiple groups of people/administrators you would want to control their password requirements. However, each policy you created in the Fine-Grained Password, it follows based on the priority level, you would need to take note on it. Keep it minimum on the policies.
Not all domain/forest functional levels support this feature of fine-grained password policy. You can refer back to the articles I have in here at the references, below.
References:
