Good day everyone. Even with the Covid-19 is rising drastically in Malaysia, kind of brings my hopes down. Anyway, I still have to keep going with life.
Today’s topic is about the Azure’s conditional access policy. We found a bug in conditional access for iOS device platform. So basically our situation is that, if we would need the conditional app control to be functioning in the Cloud App Security, we would need to setup a conditional access policy. Our setup was only to achieve monitoring mode only. However, after enabling the policy we retrieve reports saying that all iOS devices are having trouble accessing their exchange online. Users are receiving an email notification, stating that their exchange online access is being blocked. We had to disable the policy temporary to troubleshoot it.
This was the email notification:
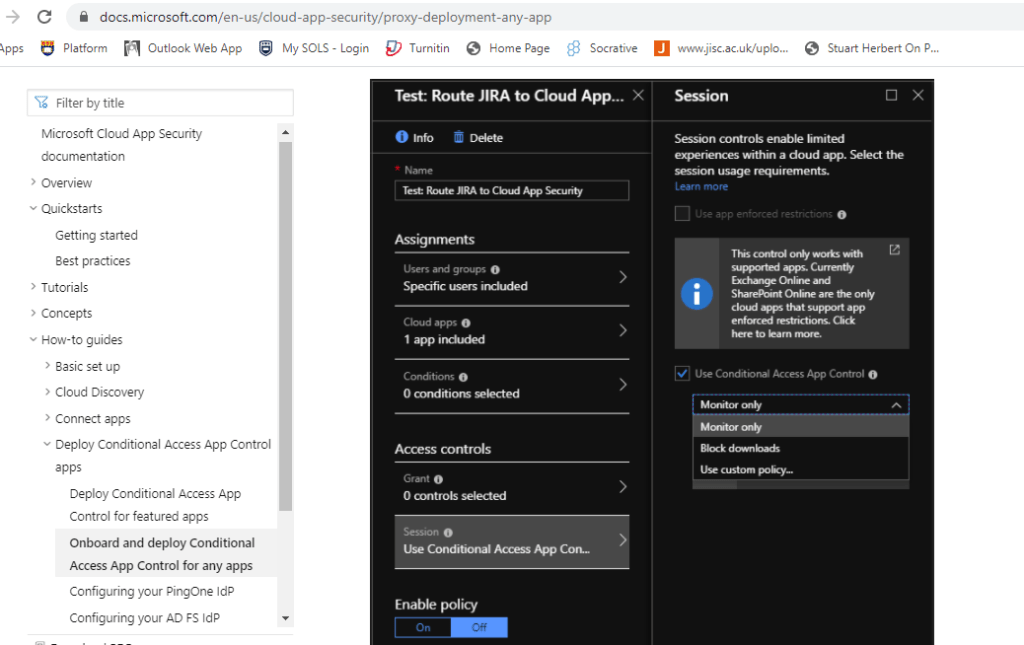
- This was our configuration for the conditional access policy;
- Assignment: Include a test group, Exclude the VIP accounts
- Cloud apps: All cloud apps
- Conditions: None
- Session: Use conditional app control (Monitor Only)
So this is the Microsoft article shows how the configuration/enablement is being setup in the conditional access in order for the app control to work, as you can see there weren’t any conditions being setup. Hence, it should not be doing any requirements checking or blocking.

To be honest, I had raise ticket to MCAS, Exchange Online and Azure team, and none of them able to get back to me an answers. MCAS team state that “no conditions are setup it SHOULD NOT be performing blocking”.
I had to stop relying the Microsoft Support for this case, as I had to find a way to identify it. So based on the image above, we can see that the article is not mature enough, because there weren’t any solid references or notes stating the limitations/restriction of monitor only of conditional app control.
Upon further checking, I had to analyze the logs of Azure Sign-in activity and Cloud App Security Activity log of that user whom experience the issue. We notice that the sign-in was shown as “Interrupted” and there was no failure sign in status. For your information, the iOS version is 14.
Error code 1: This is not an error – this is an interrupt that triggers device authentication when required due to a Conditional Access policy or because the application or resource requested the device ID in a token. This code alone does not indicate a failure on your users part to sign in. The sign in logs may indicate that the device authentication challenge was passed succesfully or failed.
Error code 2 : This is an expected part of the login flow, where a user is asked if they want to remain signed into this browser to make further logins easier. For more details, see https://techcommunity.microsoft.com/t5/Azure-Active-Directory/The-new-Azure-AD-sign-in-and-Keep-me-signed-in-experiences/td-p/128267
Error code 3: 50097
Another finding was that there weren’t any Exchange mobile device access policy/rules being configure to perform the blocking.
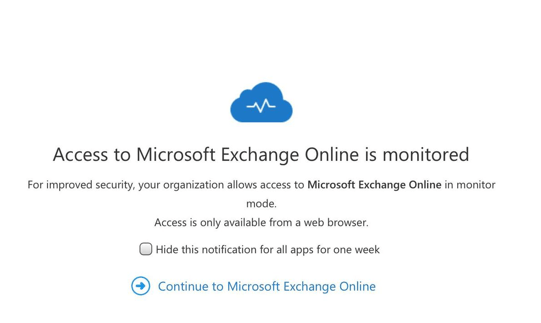
I do know that once this conditional app control is enabled there will have this prompt page before entering into the Exchange online, this is my iPad Air by the way, running on the latest version. The prompt page can be turn off though. Anyway, that is not the case here. I ran a test to mimic the situation but I didn’t experience any email notification send to me stating my exchange online access is being blocked. There is no MFA or Biometric setup on my iPad.
The questions still lies is there a pre-requisites for iOS devices for conditional access policy, even though there is no conditions being set?
Below is image from web browser;
Below image from my iOS outlook app;

Do you already have an solution found for this?
We’re now running at the same as I can see now.
LikeLike